Blog
- Home |
- Blog
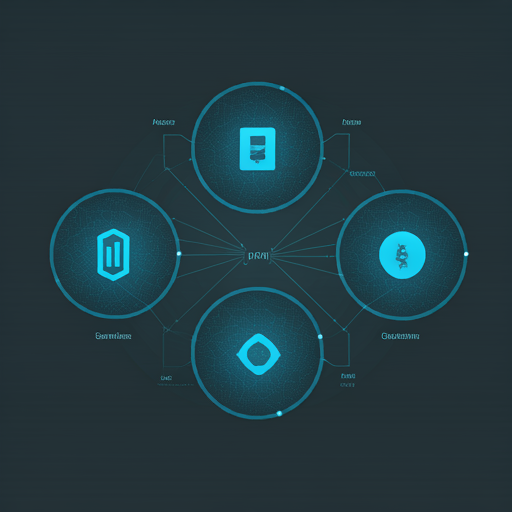
Introduction to Blockchain Technology and Cryptocurrencies
What is Blockchain Technology? Blockchain technology is the backbone of cryptocurrencies, and its potential extends far beyond just digital currency. At its simplest,...
Cross-Site Scripting (XSS)
Cross-Site Scripting (XSS): A Comprehensive Guide Introduction Cross-Site Scripting (XSS) is one of the most prevalent and dangerous vulnerabilities found in web applications....
Off-The-Shelf CMS Exploitation
Off-The-Shelf CMS Exploitation: An In-Depth Analysis Introduction Content Management Systems (CMS) have revolutionized the way websites are built, maintained, and updated. Platforms like...
Vulnerability Assessment Analyst: An In-Depth Overview
Vulnerability Assessment Analyst: An In-Depth Overview Introduction In today's digital landscape, the threat of cyberattacks looms larger than ever. Organizations are increasingly recognizing...
Deepfake Technology, Understanding and Prevention
Introduction In recent years, deepfake technology has emerged as a revolutionary yet controversial development in the realm of artificial intelligence (AI) and multimedia....
Serverless Applications and Architecture
Introduction The evolution of cloud computing has transformed how applications are built, deployed, and managed. Among the most significant advancements in this domain...
The Internet of Behavior (IoB): Transforming Data into Insights
Introduction The Internet of Behavior (IoB) is an innovative concept that merges the realms of technology, data analysis, and behavioral science. It encompasses...
Understanding Remote Access Scams, what You Need to Know
In the digital age, remote access scams have emerged as a prevalent threat, targeting unsuspecting individuals and businesses. These scams exploit the trust...